37+ data flow diagram for cloud computing Security flow data cyber event logging diagram internet logs important why so together showing concerning events au putting Computing inspirationseek data flow diagram for cloud computing security
GitHub - megrilz/Project_1_Cloud_Security: Cloud Security: Linux
Cloud computing diagram stock background Cloud computing architecture — a blueprint of cloud infrastructure Microsoft graph security api data flow
A better cloud access security broker: securing your saas cloud apps
Data flow diagram data security, png, 1506x1128px, diagram, areaCloud security: understanding the shared responsibility model layots Cloud computing diagramCloud computing security architecture.
Security microsoft cloud app access broker saas apps securing better services diagram webCloud computing network diagram where is my cloud data stored Introduction to cloud computing architectureData flow diagram in software engineering.

Security architecture design
Cloud computing security architectureCloud computing deployment models services diagram layout virtualization benefits network simple computer informationq Cloud computingA comprehensive guide to cloud security.
Cloud nube computing connectivity workloads aws beneficios azure avantages sicherheit sicurezza compliance microsoft securing kinstaSecurity data flow mapping diagrams better way Implementation computing security adaptedCloud computing diagram stock vector. illustration of mobility.

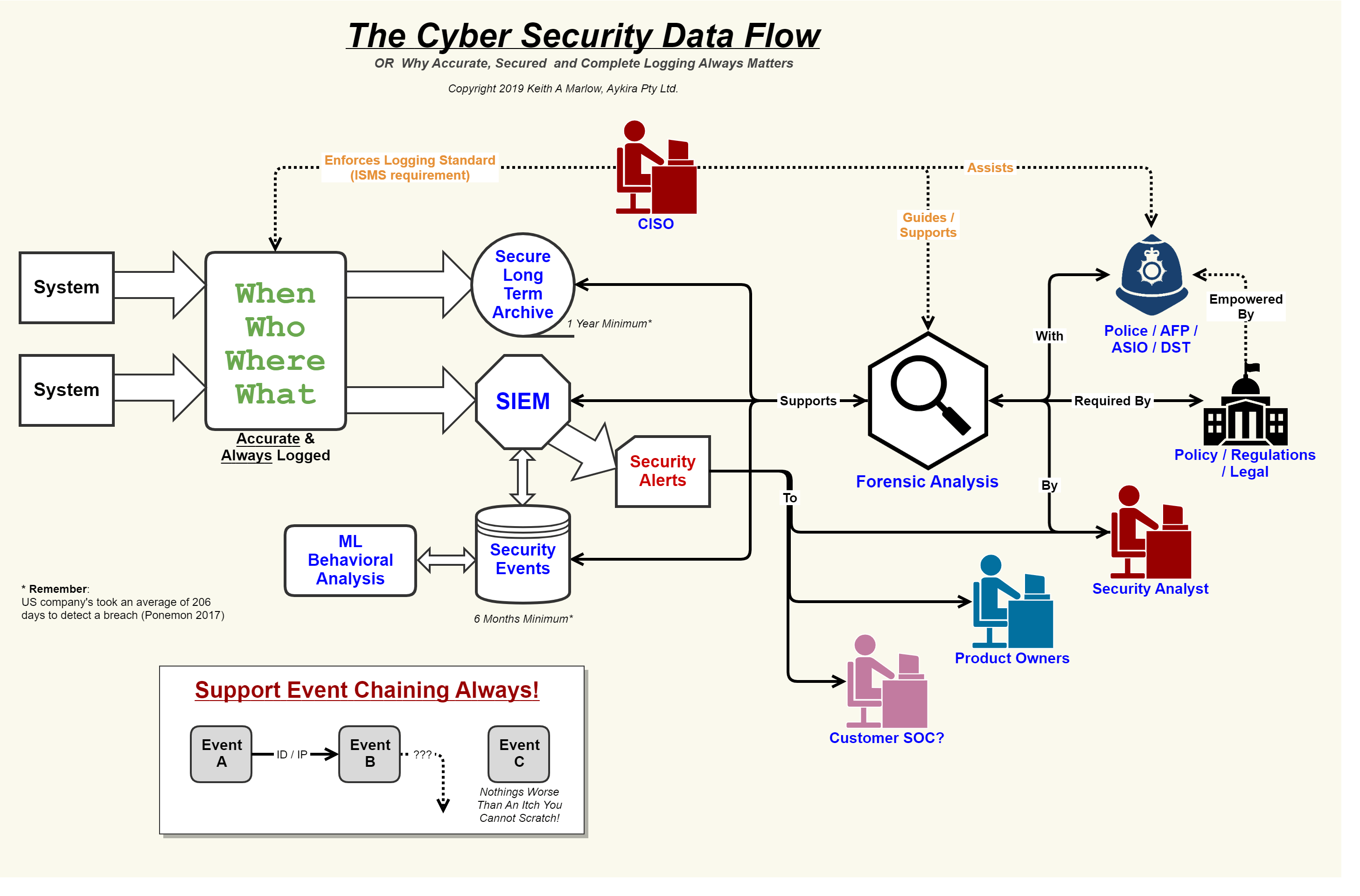
Data flow and security overview
Security network diagram architecture firewall example computer diagrams cyber clipart model networks conceptdraw recommended microsoft access examples solution devices infrastructureData flow diagram Responsibility technologiesWhat is private cloud computing?.
The data security scheme for cloud computingData flow: creating a bbm enterprise conference It security solutionsGoogle cloud architecture guide.

Data security issues and challenges in cloud computing: a conceptual
Data flow diagram37+ data flow diagram for cloud computing Security event logging, why it is so important – aykira internet solutionsCloud computing security architecture.
5 cornerstones to a successful cybersecurity programSecurity architecture review of a cloud native environment Networks diagrams encryption conceptdraw system flow controls protect explain premise flowchart san defines policies communications users audit flowchartsLibreoffice draw network diagram template.

Data flow diagrams
Cloud architecture computing infrastructure blueprint end front medium figGoogle cloud data big dataflow bigquery platform lifecycle capabilities compute processing services service engine stages public beta adds water simplified Google cloud platform blog: big data, the cloud wayCloud computing architecture introduction example computer diagrams work networks details.
Network security diagrams .